Nextcloud: Difference between revisions
Created page with "= Prerequisite = * Nginx == Install == === Add Repository === In order to get an up-to-date ownCloud, it is preferable to install it from the upstream repositories. Use..." |
Update Nginx conf for Nextcloud 12 |
||
| (19 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
= Prerequisite = | = Prerequisite = | ||
* [[Nginx]] | * [[Nginx]] | ||
* [[PHP]] | |||
* [[MariaDB]] | |||
== Install == | == Install == | ||
=== | === Download === | ||
Download Nextcloud from https://nextcloud.com/install/#instructions-server and extract the archive in <code>/var/www/nextcloud</code>. | |||
Fix file permissions using<syntaxhighlight lang="console"> | |||
$ | $ sudo chown -r www-data: /var/www/nextcloud/ | ||
</syntaxhighlight> | |||
$ sudo tee "/ | === Configure PHP === | ||
> | {{PHP/open_basedir|folders=/var/www/nextcloud/:/dev/:/var/log/nextcloud/}} | ||
> | |||
=== Configure Webserver === | |||
{{Nginx/New Site|domain=nextcloud.example.org|config=server { | |||
include snippets/listen-http.conf; | |||
server_name nextcloud.example.org; | |||
access_log /var/log/nginx/nextcloud.example.org.access.log; | |||
error_log /var/log/nginx/nextcloud.example.org.error.log; | |||
include snippets/https-permanent-redirect.conf; | |||
} | |||
server { | |||
include snippets/listen-https.conf; | |||
server_name nextcloud.example.org; | |||
access_log /var/log/nginx/nextcloud.example.org.access.log; | |||
error_log /var/log/nginx/nextcloud.example.org.error.log; | |||
include snippets/acme-challenge.conf; | |||
#include snippets/ssl.conf; | |||
#ssl_certificate /etc/letsencrypt/live/nextcloud.example.org/fullchain.pem; | |||
#ssl_certificate_key /etc/letsencrypt/live/nextcloud.example.org/privkey.pem; | |||
#include snippets/hsts.conf; | |||
# Protect web interface during initial setup | |||
# The following two lines must be removed after initial configuration | |||
auth_basic "You shall not pass!"; | |||
auth_basic_user_file /etc/nginx/htpasswd/generic.htpasswd; | |||
include snippets/security-headers.conf; | |||
# Using more_set_headers instead of add_header to be cascaded in sub location | |||
more_set_headers "X-Robots-Tag: none"; | |||
more_set_headers "X-Download-Options: noopen"; | |||
# Path to the root of your installation | |||
root /var/www/nextcloud/; | |||
location = /.well-known/carddav { | |||
return 301 $scheme://$host/remote.php/dav; | |||
} | |||
location = /.well-known/caldav { | |||
return 301 $scheme://$host/remote.php/dav; | |||
} | |||
client_max_body_size 10G; # set max upload size | |||
fastcgi_buffers 64 4K; | |||
location / { | |||
rewrite ^ /index.php$uri; | |||
} | |||
location ~ ^/(?:build{{!}}tests{{!}}config{{!}}lib{{!}}3rdparty{{!}}templates{{!}}data)/ { | |||
deny all; | |||
} | |||
location ~ ^/(?:\.{{!}}autotest{{!}}occ{{!}}issue{{!}}indie{{!}}db_{{!}}console) { | |||
deny all; | |||
} | |||
location ~ ^/(?:index{{!}}remote{{!}}public{{!}}cron{{!}}core/ajax/update{{!}}status{{!}}ocs/v[12]{{!}}updater/.+{{!}}ocs-provider/.+)\.php(?:${{!}}/) { | |||
fastcgi_split_path_info ^(.+\.php)(/.+)$; | |||
include fastcgi_params; | |||
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name; | |||
fastcgi_param PATH_INFO $fastcgi_path_info; | |||
fastcgi_param HTTPS on; | |||
fastcgi_param modHeadersAvailable true; #Avoid sending the security headers twice | |||
fastcgi_param front_controller_active true; | |||
fastcgi_pass php; | |||
fastcgi_intercept_errors on; | |||
fastcgi_request_buffering off; | |||
} | |||
location ~ ^/(?:updater{{!}}ocs-provider)(?:${{!}}/) { | |||
try_files $uri/ =404; | |||
index index.php; | |||
} | |||
# Adding the cache control header for js and css files | |||
# Make sure it is BELOW the PHP block | |||
location ~* \.(?:css{{!}}js{{!}}woff{{!}}svg{{!}}gif)$ { | |||
try_files $uri /index.php$uri$is_args$args; | |||
add_header Cache-Control "public, max-age=15778463"; | |||
} | |||
location ~* \.(?:png{{!}}html{{!}}ttf{{!}}ico{{!}}jpg{{!}}jpeg)$ { | |||
try_files $uri /index.php$uri$is_args$args; | |||
} | |||
<nowiki>}</nowiki> | |||
}} | |||
=== Configure Nextcloud === | |||
//config.php<syntaxhighlight lang="console"> | |||
$ sudo tee "/usr/local/bin/occ" > /dev/null << EOF | |||
> !/bin/sh | |||
> sudo -u www-data /usr/bin/php /var/www/nextcloud/occ "\$@" | |||
> EOF | > EOF | ||
$ sudo | $ sudo chmod +x /usr/local/bin/occ | ||
</syntaxhighlight> | </syntaxhighlight> | ||
=== | === Logs === | ||
<syntaxhighlight lang="console"> | First you need to create a folder for the logs<syntaxhighlight lang="console"> | ||
$ sudo | $ sudo mkdir /var/log/nextcloud | ||
$ sudo chmod 750 /var/log/nextcloud | |||
$ sudo chown www-data:adm /var/log/nextcloud | |||
</syntaxhighlight>Create file <code>/etc/logrotate.d/nextcloud</code> with the following content<syntaxhighlight lang="text"> | |||
/var/log/nextcloud/nextcloud.log { | |||
rotate 6 | |||
monthly | |||
compress | |||
delaycompress | |||
missingok | |||
notifempty | |||
create 640 www-data adm | |||
} | |||
</syntaxhighlight>Finally activate the new log location. Edit <code>/var/www/nextcloud/config/config.php</code> and add/edit the <code>logfile</code> line<syntaxhighlight lang="php"> | |||
'logfile' => '/var/log/nextcloud/nextcloud.log', | |||
</syntaxhighlight> | </syntaxhighlight> | ||
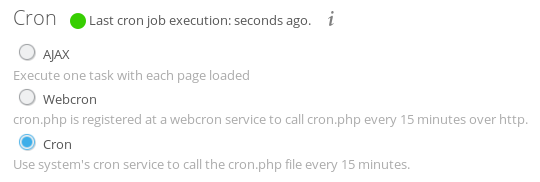
=== Cron === | |||
Create file <code>/etc/cron.d/nextcloud</code><syntaxhighlight lang="text"> | |||
*/15 * * * * www-data /usr/bin/php -f /var/www/nextcloud/cron.php | |||
</syntaxhighlight>Now open Nextcloud in your browser and go to the admin section and activate cron | |||
[[File:owncloud cron.png|border|frameless|540x540px]] | |||
== Test == | |||
=== Security === | |||
Nextcloud is providing a [https://scan.nextcloud.com/ security scanning service] for public instances. Scan your instance to find configuration issues. | |||
[[Category:Debian Release]] | [[Category:Debian Release]] | ||
[[Category:Linux Server]] | [[Category:Linux Server]] | ||
Latest revision as of 07:37, 4 October 2017
Prerequisite
Install
Download
Download Nextcloud from https://nextcloud.com/install/#instructions-server and extract the archive in /var/www/nextcloud.
Fix file permissions using
$ sudo chown -r www-data: /var/www/nextcloud/
Configure PHP
Edit file /etc/php/7.0/mods-available/local-common.ini and add /var/www/nextcloud/:/dev/:/var/log/nextcloud/ to the open_basedir setting.
Reload PHP:
$ sudo systemctl reload php7.0-fpm.service
Configure Webserver
- Create the config file
/etc/nginx/sites-available/nextcloud.example.orgserver { include snippets/listen-http.conf; server_name nextcloud.example.org; access_log /var/log/nginx/nextcloud.example.org.access.log; error_log /var/log/nginx/nextcloud.example.org.error.log; include snippets/https-permanent-redirect.conf; } server { include snippets/listen-https.conf; server_name nextcloud.example.org; access_log /var/log/nginx/nextcloud.example.org.access.log; error_log /var/log/nginx/nextcloud.example.org.error.log; include snippets/acme-challenge.conf; #include snippets/ssl.conf; #ssl_certificate /etc/letsencrypt/live/nextcloud.example.org/fullchain.pem; #ssl_certificate_key /etc/letsencrypt/live/nextcloud.example.org/privkey.pem; #include snippets/hsts.conf; # Protect web interface during initial setup # The following two lines must be removed after initial configuration auth_basic "You shall not pass!"; auth_basic_user_file /etc/nginx/htpasswd/generic.htpasswd; include snippets/security-headers.conf; # Using more_set_headers instead of add_header to be cascaded in sub location more_set_headers "X-Robots-Tag: none"; more_set_headers "X-Download-Options: noopen"; # Path to the root of your installation root /var/www/nextcloud/; location = /.well-known/carddav { return 301 $scheme://$host/remote.php/dav; } location = /.well-known/caldav { return 301 $scheme://$host/remote.php/dav; } client_max_body_size 10G; # set max upload size fastcgi_buffers 64 4K; location / { rewrite ^ /index.php$uri; } location ~ ^/(?:build|tests|config|lib|3rdparty|templates|data)/ { deny all; } location ~ ^/(?:\.|autotest|occ|issue|indie|db_|console) { deny all; } location ~ ^/(?:index|remote|public|cron|core/ajax/update|status|ocs/v[12]|updater/.+|ocs-provider/.+)\.php(?:$|/) { fastcgi_split_path_info ^(.+\.php)(/.+)$; include fastcgi_params; fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name; fastcgi_param PATH_INFO $fastcgi_path_info; fastcgi_param HTTPS on; fastcgi_param modHeadersAvailable true; #Avoid sending the security headers twice fastcgi_param front_controller_active true; fastcgi_pass php; fastcgi_intercept_errors on; fastcgi_request_buffering off; } location ~ ^/(?:updater|ocs-provider)(?:$|/) { try_files $uri/ =404; index index.php; } # Adding the cache control header for js and css files # Make sure it is BELOW the PHP block location ~* \.(?:css|js|woff|svg|gif)$ { try_files $uri /index.php$uri$is_args$args; add_header Cache-Control "public, max-age=15778463"; } location ~* \.(?:png|html|ttf|ico|jpg|jpeg)$ { try_files $uri /index.php$uri$is_args$args; } }
- Activate the configuration with
$ sudo nginx_modsite -e nextcloud.example.org Would you like to reload the Nginx configuration now? (Y/n) Y
- Edit file
/usr/local/etc/certmanage/main.jsonand add the following to the list{ "domains": ["nextcloud.example.org"], "reload": [["/bin/systemctl", "reload", "nginx.service"]] }
- Get your certificate
$ sudo /usr/local/sbin/certmanage Renewing certificate for nextcloud.example.org that will expire on 0001-01-01 Saving debug log to /var/log/letsencrypt/letsencrypt.log Starting new HTTPS connection (1): acme-v01.api.letsencrypt.org Obtaining a new certificate Performing the following challenges: http-01 challenge for nextcloud.example.org Using the webroot path /var/www/acme-challenge for all unmatched domains. Waiting for verification... Cleaning up challenges Generating key (2048 bits): /etc/letsencrypt/keys/1764_key-certbot.pem Creating CSR: /etc/letsencrypt/csr/1764_csr-certbot.pem IMPORTANT NOTES: - Congratulations! Your certificate and chain have been saved at /etc/letsencrypt/live/nextcloud.example.org/fullchain.pem. Your cert will expire on 2026-07-22. To obtain a new or tweaked version of this certificate in the future, simply run certbot again. To non-interactively renew *all* of your certificates, run "certbot renew" - If you like Certbot, please consider supporting our work by: Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate Donating to EFF: https://eff.org/donate-le Restarting services: systemctl reload nginx.service
- Uncomment the ssl related lines in
/etc/nginx/sites-available/nextcloud.example.organd run$ sudo systemctl reload nginx.service
Configure Nextcloud
//config.php
$ sudo tee "/usr/local/bin/occ" > /dev/null << EOF
> !/bin/sh
> sudo -u www-data /usr/bin/php /var/www/nextcloud/occ "\$@"
> EOF
$ sudo chmod +x /usr/local/bin/occ
Logs
First you need to create a folder for the logs
$ sudo mkdir /var/log/nextcloud
$ sudo chmod 750 /var/log/nextcloud
$ sudo chown www-data:adm /var/log/nextcloud
Create file /etc/logrotate.d/nextcloud with the following content
/var/log/nextcloud/nextcloud.log {
rotate 6
monthly
compress
delaycompress
missingok
notifempty
create 640 www-data adm
}
Finally activate the new log location. Edit /var/www/nextcloud/config/config.php and add/edit the logfile line
'logfile' => '/var/log/nextcloud/nextcloud.log',
Cron
Create file /etc/cron.d/nextcloud
*/15 * * * * www-data /usr/bin/php -f /var/www/nextcloud/cron.php
Now open Nextcloud in your browser and go to the admin section and activate cron
Test
Security
Nextcloud is providing a security scanning service for public instances. Scan your instance to find configuration issues.