Nextcloud
Prerequisite
Install
Add Repository
In order to get an up-to-date ownCloud, it is preferable to install it from the upstream repositories.
Use the following command to install the repository and its key, plus to configure pinning to use it as the default source
$ curl -s https://download.owncloud.org/download/repositories/stable/Debian_8.0/Release.key | sudo apt-key add -
OK
$ echo "deb http://download.owncloud.org/download/repositories/stable/Debian_8.0/ /" | sudo tee /etc/apt/sources.list.d/owncloud.list > /dev/null
$ sudo tee "/etc/apt/preferences.d/owncloud" > /dev/null << EOF
> Package: owncloud
> Pin: origin "download.owncloud.org"
> Pin-Priority: 995
> EOF
$ sudo apt update
Install
$ sudo apt install owncloud
Configure PHP
Edit file /etc/php5/mods-available/local-common.ini and add /var/www/nextcloud/:/dev/:/var/log/nextcloud/ to the open_basedir setting.
Reload PHP:
$ sudo service php5-fpm reload
Configure Webserver
- Create the config file
/etc/nginx/sites-available/owncloud.example.orgserver server server { include snippets/listen-http.conf; server_name owncloud.example.org; access_log /var/log/nginx/owncloud.example.org.access.log; error_log /var/log/nginx/owncloud.example.org.error.log; include snippets/https-permanent-redirect.conf; } server { include snippets/listen-https.conf; server_name owncloud.example.org; access_log /var/log/nginx/owncloud.example.org.access.log; error_log /var/log/nginx/owncloud.example.org.error.log; include snippets/acme-challenge.conf; #include snippets/ssl.conf; #ssl_certificate /etc/letsencrypt/live/owncloud.example.org/fullchain.pem; #ssl_certificate_key /etc/letsencrypt/live/owncloud.example.org/privkey.pem; #include snippets/hsts.conf; # Protect web interface during initial setup # The following two lines must be removed after initial configuration auth_basic "You shall not pass!"; auth_basic_user_file /etc/nginx/htpasswd/generic.htpasswd; include snippets/security-headers.conf; include snippets/x-frame-options-sameorigin.conf; add_header X-Robots-Tag none always; add_header X-Download-Options noopen always; # Path to the root of your installation root /var/www/owncloud/; location = /.well-known/carddav { return 301 $scheme://$host/remote.php/dav; } location = /.well-known/caldav { return 301 $scheme://$host/remote.php/dav; } client_max_body_size 10G; # set max upload size fastcgi_buffers 64 4K; error_page 403 /core/templates/403.php; error_page 404 /core/templates/404.php; location / { rewrite ^ /index.php$uri; } location ~ ^/(?:build|tests|config|lib|3rdparty|templates|data)/ { return 404; } location ~ ^/(?:\.|autotest|occ|issue|indie|db_|console) { return 404; } location ~ ^/(?:index|remote|public|cron|core/ajax/update|status|ocs/v[12]|updater/.+|ocs-provider/.+|core/templates/40[34])\.php(?:$|/) { fastcgi_split_path_info ^(.+\.php)(/.+)$; include fastcgi_params; fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name; fastcgi_param PATH_INFO $fastcgi_path_info; fastcgi_param HTTPS on; fastcgi_param modHeadersAvailable true; #Avoid sending the security headers twice fastcgi_param front_controller_active true; fastcgi_pass unix:/var/run/php5-fpm.sock; fastcgi_intercept_errors on; fastcgi_request_buffering off; } location ~* \.(?:css|js)$ { try_files $uri /index.php$uri$is_args$args; add_header Cache-Control "public, max-age=7200"; } location ~* \.(?:svg|gif|png|html|ttf|woff|ico|jpg|jpeg)$ { try_files $uri /index.php$uri$is_args$args; } location ~* ^.+\.(jpg|jpeg|gif|bmp|ico|png|css|js|swf|svg)$ { expires 30d; } }
- Activate the configuration with
$ sudo nginx_modsite -e owncloud.example.org Would you like to reload the Nginx configuration now? (Y/n) Y
- Edit file
/usr/local/etc/certmanage/main.jsonand add the following to the list{ "domains": ["owncloud.example.org"], "reload": [["/bin/systemctl", "reload", "nginx.service"]] }
- Get your certificate
$ sudo /usr/local/sbin/certmanage Renewing certificate for owncloud.example.org that will expire on 0001-01-01 Saving debug log to /var/log/letsencrypt/letsencrypt.log Starting new HTTPS connection (1): acme-v01.api.letsencrypt.org Obtaining a new certificate Performing the following challenges: http-01 challenge for owncloud.example.org Using the webroot path /var/www/acme-challenge for all unmatched domains. Waiting for verification... Cleaning up challenges Generating key (2048 bits): /etc/letsencrypt/keys/1764_key-certbot.pem Creating CSR: /etc/letsencrypt/csr/1764_csr-certbot.pem IMPORTANT NOTES: - Congratulations! Your certificate and chain have been saved at /etc/letsencrypt/live/owncloud.example.org/fullchain.pem. Your cert will expire on 2026-07-20. To obtain a new or tweaked version of this certificate in the future, simply run certbot again. To non-interactively renew *all* of your certificates, run "certbot renew" - If you like Certbot, please consider supporting our work by: Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate Donating to EFF: https://eff.org/donate-le Restarting services: systemctl reload nginx.service
- Uncomment the ssl related lines in
/etc/nginx/sites-available/owncloud.example.organd run$ sudo systemctl reload nginx.service
Configure ownCloud
//config.php
$ sudo tee "/usr/local/bin/occ" > /dev/null << EOF
> !/bin/sh
> sudo -u www-data /usr/bin/php /var/www/nextcloud/occ "\$@"
> EOF
$ sudo chmod +x /usr/local/bin/occ
Logs
First you need to create a folder for the logs
$ sudo mkdir /var/log/nextcloud
$ sudo chmod 750 /var/log/nextcloud
$ sudo chown www-data:adm /var/log/nextcloud
Create file /etc/logrotate.d/nextcloud with the following content
/var/log/nextcloud/nextcloud.log {
rotate 6
monthly
compress
delaycompress
missingok
notifempty
create 640 www-data adm
}
Finally activate the new log location. Edit /var/www/nextcloud/config/config.php and add/edit the logfile line
'logfile' => '/var/log/nextcloud/nextcloud.log',
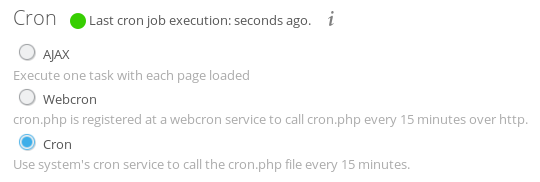
Cron
Create file /etc/cron.d/nextcloud
*/15 * * * * www-data /usr/bin/php -f /var/www/nextcloud/cron.php
Now open Nextcloud in your browser and go to the admin section and activate cron
Fail2Ban
Create file /etc/fail2ban/filter.d/owncloud.conf
[Definition]
failregex="Login failed: '.*' \(Remote IP: '<HOST>'?\)"
Create file /etc/fail2ban/jail.d/owncloud.conf
[owncloud]
enabled = true
filter = owncloud
port = http,https
logpath = /var/log/owncloud/owncloud.log
Finally, activate the new jail using
$ sudo fail2ban-client reload owncloud
ERROR NOK: ('owncloud',)
(the error message is normal)